What is Browser Fingerprinting and why is it used?
Browser Fingerprinting is often seen as an alternative to using Cookies to identify individual users online. There are similarities in the two approaches, but important differences too. Whereas Cookie-based identifiers will just save a unique ID to the user’s browsers, Browser Fingerprinting tries to identify a user based on the specific combination of variables and settings that each of our browsers shares.
Why try to identify users?
Identifying whether a request has come from a user that has previously visited a site has a whole range of applications; ranging from security to analytics. Fingerprinting is though most often discussed in the context of advertising technology, where some providers use it to identify users as they visit different websites, building up a profile of their interests.
Why not use Web Cookies?
Browser fingerprinting is most frequently seen as an alternative when Cookies are either too unreliable or too limiting. The recent upturn in interest around Browser Fingerprinting is largely attributed to more prevalent blocking of Cookies by browsers.
Is Browser Fingerprinting a good thing?
Whilst Browser Fingerprinting can often be abused to violate the privacy of users, it also has many good applications. It is still widely used for its initial purpose in security and authentification online. For example, to prevent identity theft and online fraud. However, whilst Fingerprinting has great value in areas such as fraud prevention, its use for applications such as behavioural tracking is a concern to many. Where Cookies can be controlled by the user, the same cannot easily be done with Browser Fingerprinting.
Is Browser Fingerprinting accurate?
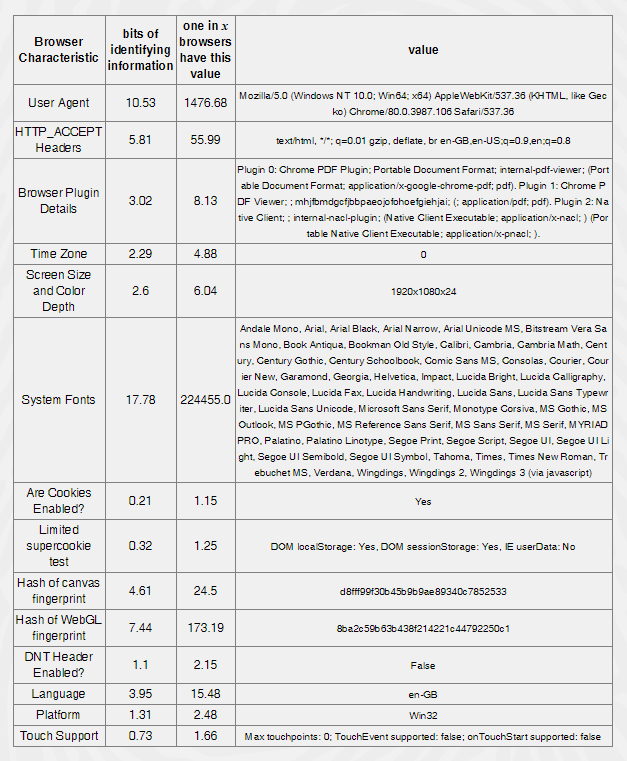
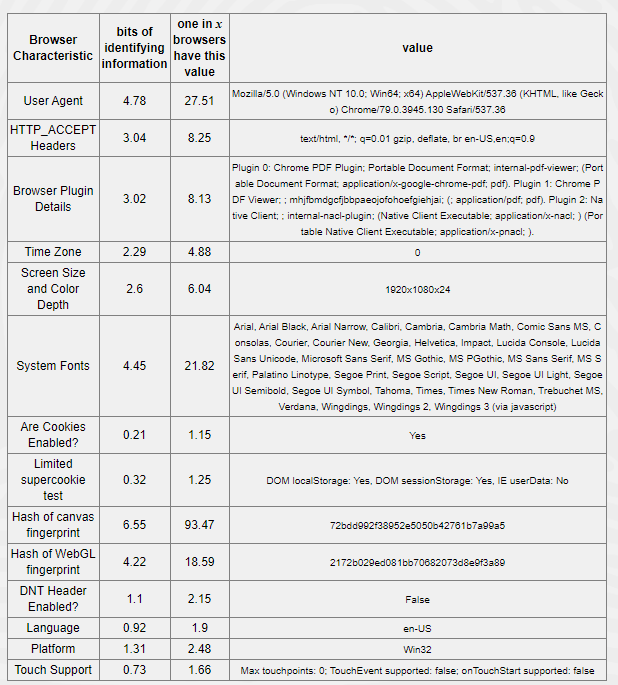
Many people are surprised by how well browser fingerprinting can differentiate between users. We used Panoptclick to report on the device fingerprints of two machines in our office. Both are very similar hardware, running on the same network and installed with largely the same software, yet both machines generated uniquely identifiable fingerprints.
Some example pieces of browser identification points include time zone, browser plugin details, cookie consent, language, screen size and colour depth. In the example below, you can see that despite using the same device, each has been configured with a slightly different setup.
You can view your device fingerprint and analyse whether your browser and add-ons protect you against online tracking techniques here.
Why is Browser Fingerprinting a threat to online privacy?
Browser Fingerprinting as a tracking technique makes Third-Party Cookies look relatively tame. This is because Web Cookies are deliberately limited in scope, their use blockable and users are able to control cookies or delete cookies. However, Browser Fingerprinting is difficult for users to detect and even more tough for browsers to combat.
A common method of data collection in Browser Fingerprinting is through users clicking social sharing buttons. Whilst the aforementioned data points may seem relatively generic, it’s extremely valuable to advertisers and the likelihood of another user sharing the same characteristics as you are virtually slim to none. In fact, Panopticlick found that just one in every 286,777 browsers share that same fingerprint.
What does the future hold for Browser Fingerprinting?
In recent years, increased public concern for internet privacy has propelled users to regain control over their online data. Given the opaque nature of Browser Fingerprinting, it is likely that as awareness grows, more and more users will also be opposed to this particular type of identifier.
We anticipate that in the future even more browsers will implement anti-fingerprinting measures so that sites cannot identify you. Certain browsers, such as Apple’s Safari and Mozilla have already implemented these anti-tracking measures. The recent focus on privacy has given other browsers a competitive edge against Chrome, who currently owns around two-thirds of market share.
Google has now also announced that User-Agent Strings are to be deprecated in Chrome, meaning that Browser Fingerprinting will share the same fate as Third-Party Cookies. User-Agent Strings are pieces of information that are sent out by your browser to the website you are visiting, such as browser, version and operating system. Browser Fingerprinting relies upon the information collected from User-Agent Strings and this move will hinder its functionality. However, according to their Privacy Sandbox project, Google hopes to replace the functionality of User-Agent Strings with User-Agent Client Hits (UACH).